| Job Title | Average Wage | Annual Job Openings | Expected Growth |
| Information Security Analyst | MT: $79,200/yr US: $102,600/yr |
MT: No data available US: 16,300 |
MT: No data available US: 33% |
*Information obtained from O*NET OnLine
Cybersecurity A.A.S. Program Estimated Costs
Cybersecurity C.T.S. Program Estimated Costs
Figure Out Your Finances
Students seeking federal financial aid (which includes grants and loans) must complete the Free Application for Federal Student Aid (FAFSA) which online at fafsa.ed.gov. As a result of completing a FAFSA, an applicant will receive a federal Student Aid Report (SAR) in the mail or online. An electronic version of the SAR is automatically sent to the schools listed on the FAFSA. To list Great Falls College MSU, use our school code: 009314.
Students applying for financial aid may also be required to provide proper federal income tax information, completed verification materials, and any other information requested by the Financial Aid Office. Students must apply for financial aid annually.
Assistance is available to prospective students applying for financial aid. In addition, financial aid counseling for new students is an integral part of the admissions and orientation process. Once enrolled, students may receive counseling and assistance as needed. For assistance, please call 406-771-4334, or write to the Financial Aid Office, Great Falls College MSU, 2100 16th Ave S, Great Falls, MT 59405, or email finaid@gfcmsu.edu.
Great Falls College MSU also offers a wide variety of different scholarships to assist you in paying for your college. To view a list of current scholarship offerings, please see our scholarship page.
Cybersecurity A.A.S. Program Requirements
Cybersecurity C.T.S. Program Requirements
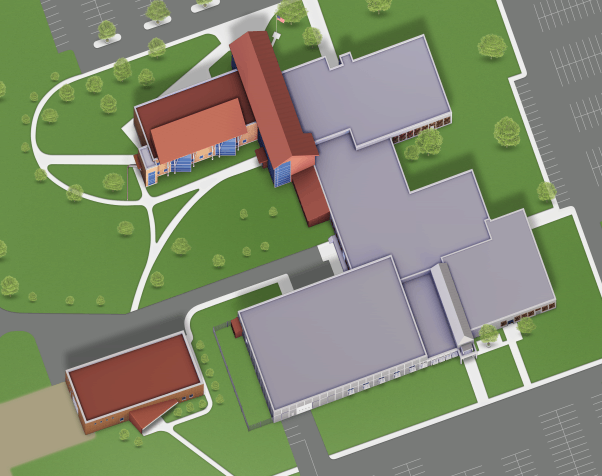
Great Falls College MSU
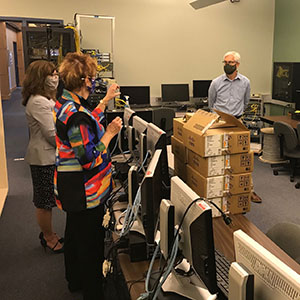
Computer Science Programs In The News
Computer Information Technology Faculty

 Welcome to Great Falls College MSU
Welcome to Great Falls College MSU